4 Steps to Easily Increase WordPress User Security

User accounts are typically protected with only a username and password, and hopefully a strong password! If you use online banking or some other account you’ve probably experienced the need to enter an additional code sent to your email or phone via text message. This additional verification is called Two-Factor Authentication (2FA), or Multi-Factor Authentication (MFA).
The goal of the additional code via 2FA is to help prove that you are the owner of the account you’re trying to login to. By providing the additional code, you are essentially proving you have control of the email address or the phone number. Typically a hacker will only have access to the username and password, so the additional factor (your email or phone) makes it harder for the hacker.
However, if you use enough accounts that have 2FA enabled, on a daily basis it can become cumbersome waiting for an email or text message, and then having to manually enter the code. This is where “security keys” can greatly help. Modern security keys are physical devices that look like a USB stick drive except they contain a secure element that securely stores private keys making it difficult to obtain them, unlike a phone that susceptible to malware.
One of the more recent developments in 2FA is the “Universal 2nd Factor” (U2F) standard that defines an interaction with a compatible-U2F device for authentication. This new protocol helps mitigate phishing and man-in-the-middle attacks where a hacker can impersonate the website you think you’re logging into and steal your credentials – despite using an additional code.
U2F sounds great. So how do we add it to WordPress? It’s surprisingly straight forward actually. We first need a WordPress site that’s already using HTTPS (U2F only works over HTTPS), a U2F security key (such as Yubikey), a recent version of the Google Chrome web browser (for now), we need to install a U2F plugin (for now we’ll be using the “Two Factor” plugin), and lastly, setup your user account for the U2F key. I say “for now” because it’s planned for the 4.5 version of WordPress to include 2FA support, however until then we need to use a plugin.
Step #1, a WordPress site that’s using HTTPS.
Your WordPress site doesn’t have HTTPS? That’s not good. Without HTTPS your credentials can already be stolen, especially if using a public network like a coffee shop’s WiFi. Plus added benefits as giving your users a lock icon of assurance and Google-boosting your search results. Contact us if you need help converting your site to HTTPS.
Step #2, a U2F device.
I recommend the Yubikey FIDO U2F Security Key because it’s well-known and cheap. You will get the best price if you have a Github account (click here to buy with your Github account). Another option is to buy through a Google Apps account (click here to buy with your Google Apps account). If neither of those are applicable to you, then you can click here to purchase it for the retail price from Amazon.
Step #3, the WordPress plugin.
At the time of this writing (March 2016), a plugin is necessary to use this functionality in WordPress. Go to Plugins, click “Add New”, search for “Two-Factor” and install the one by George Stephanis. After it’s installed, activate it.
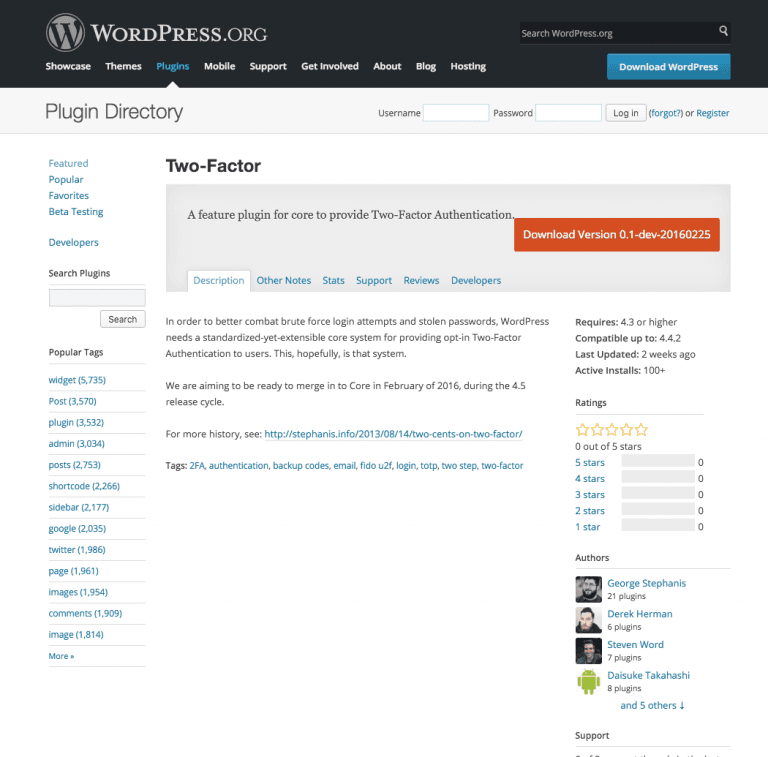
The Two-Factor plugin page from the directory.
Step #4, setup your user account.
After the plugin is activated, edit your WordPress user profile. That’s your personal profile.
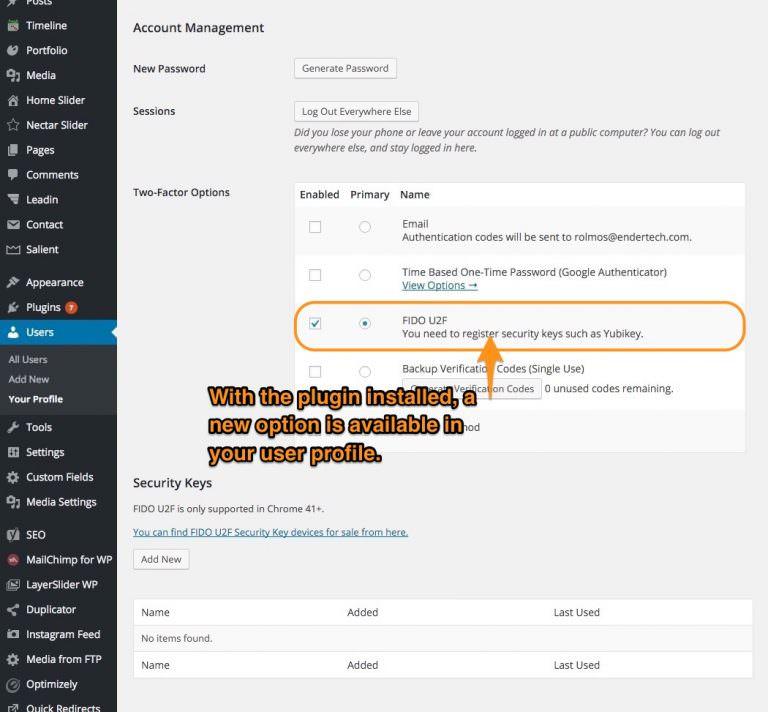
When the 2FA plugin is installed, a new section will appear in your user profile.
Near the bottom, under Account Management, you’ll see “Two-Factor Options” and “Security Keys”. Plugin your U2F security key via USB. Click the “Add New” button under “Security Keys” and it will change to “Now insert (and tap) your Security Key.” You should see your U2F security key’s light blinking. Touch your security key and your security key will be added.
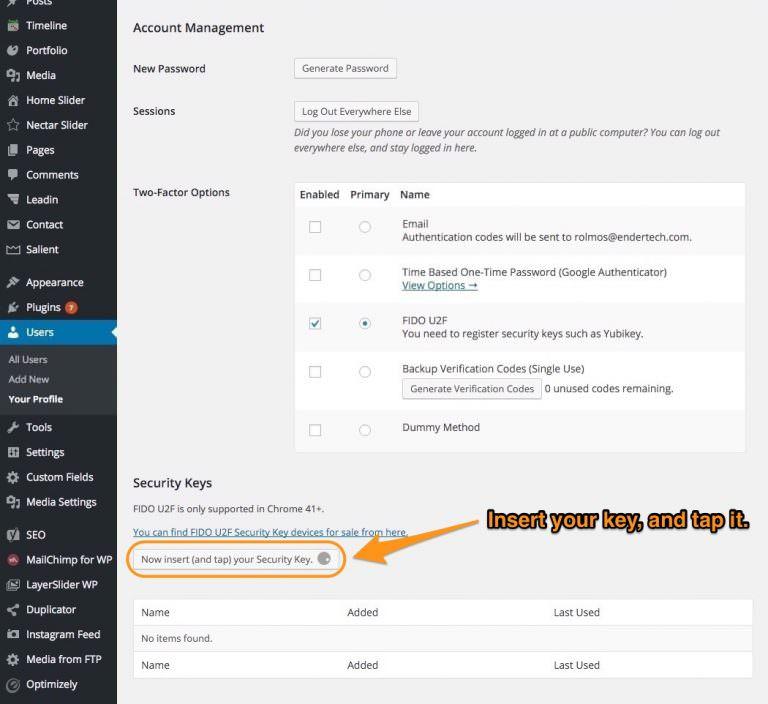
Plug your UFA device into your USB port and click “add new”. Then, insert your key and tap it.
After it’s added check the box under the “Enabled” column next to “FIDO U2F” row, and select the box for “Primary”. Save your profile. Now log out and log back in with your username and password. After logging in you’ll see “Now insert (and tap) your Security Key.”. After doing so, you’ll be fully logged in. Congrats! Much easier than manual verification codes, right?
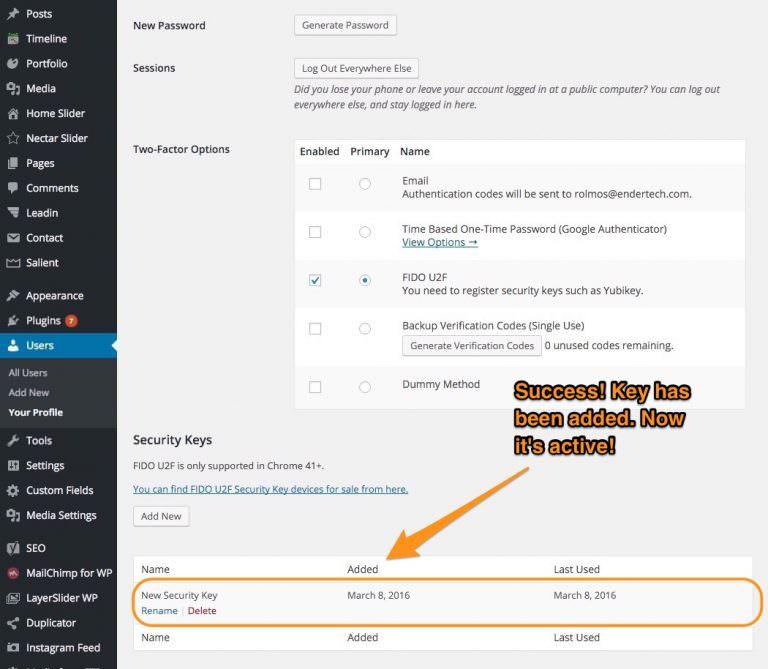
Your security key is active!
Now that you’ve seen how easy it is to use U2F, explore what other apps you use that support it. Two popular services that utilize U2F are Google Apps/Gmail and Dropbox. I recommend setting it up for them to enhance your online security by protecting your accounts with an additional layer beyond just a username and password.


The next time you sign in…
…you’ll need to insert and tap your Security Key.
Closing Thoughts
Buy two U2F devices. You should have a backup in case one gets lost or stops working. You should add both of those U2F keys to your accounts and then securely store one away.
Evaluate your options if you use your phone or a tablet to interact with these apps. If you do, you’ll probably need to use the more expensive Yubikey NEO with NFC support. Otherwise you’ll need to make sure the app can still use email or text message codes (such as how Google/Gmail does) because the U2F security key currently does not work with mobile devices. Yubico, the creator of Yubikey, is working on a mobile app that may provide a solution for that.
Endertech is a Los Angeles WordPress Developer Company able to provide solutions for your WordPress and other web development needs. Contact us for a free consultation.

